Enhance data protection with reliable cloud security solutions. Safeguard your information and maintain peace of mind.
Cloud computing is revolutionizing the digital world. It provides numerous advantages for businesses, irrespective of their size. Cloud technology has been shown to have cost-saving benefits, improve performance, and enhance business flexibility.
It is important to consider cloud security risks when organizations implement this technology. Proficiency in cloud security practices enables the protection of digital operations with confidence.
This guest post examines cloud security, addressing the business spheres required to enhance the cloud environment’s security for its proper functioning.
By acquiring the necessary knowledge and tools to protect your digital operations, you can take advantage of the cloud’s opportunities while ensuring data protection.
Cloud Computing Security: Why It’s Important for Small Businesses
Cloud computing is a modern method of delivering computing resources through the Internet with a flexible payment model based on usage. Network-based solutions offer a cost-effective substitute for managing local files and services.
Depending on the specific threats, various methods exist to manage security risks associated with cloud technology. Let’s review best practices to safeguard IT systems for all companies.

Also Read: Securing Your Cloud Data: Best Practices with AWS Elasticsearch
DevOps process
It can assist in improving code quality, reducing exploits and vulnerabilities, and speeding up software development and deployment of features.
Automated operations.
The increasing frequency and intensity of security threats are challenging cloud-based developers. Implementing automation software solutions can streamline tasks and improve the development process.
Unified control.
Revolutionize your workflow and streamline processes with a cutting-edge, centralized management system featuring an open integration fabric for ultimate control.
Regulations compliance.
It is necessary to develop policies regarding privacy and compliance that outline employee interactions and data transfer procedures. Establishing a governance framework to determine authority and responsibilities within the organization is necessary.
Moreover, regularly checking your IT system is important to prevent and detect malware attacks. Cloud servers require constant audits for security, access to reports, and vendor control.
Incorporating blockchain technology into cloud computing can enhance data security by utilizing encryption and fortified database protection to prevent potential breaches.
Related: Top 8 Cloud Services Benefits for Small Business
What business spheres need cloud security the most and why?
- Healthcare organizations face challenges with cyber risks and data breaches
- Finance and banking industries need to prioritize security
- The retail sector must create an impregnable security barrier
- The manufacturing industry’s complex, digitized environment increases cyber risks
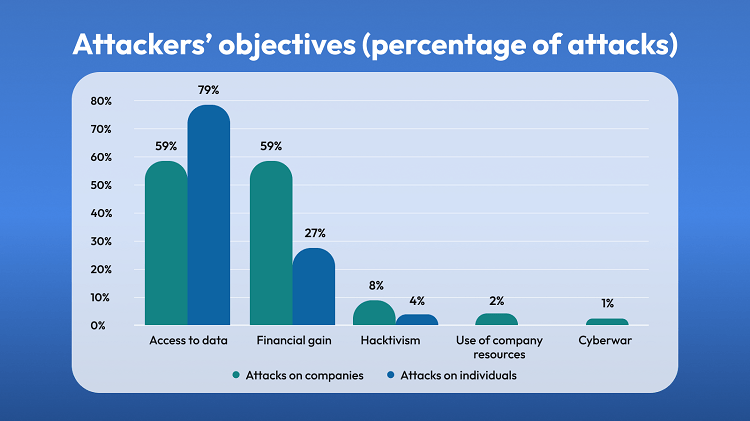
Attackers’ typical objectives with the percentage of attacks
The Importance of Secure Cloud Computing: Protecting Your Business
Although public cloud services offer several advantages, they pose new data security risks that can lead to substantial financial losses.
The widespread adoption of remote work practices has compounded these risks as cyber-attacks continue to surge in frequency and sophistication.
The studies indicate that a staggering 47% of companies have shifted a majority of their employees to work from home, with a range of 61-80% embracing remote work arrangements.
Unfortunately, this surge in remote work has also paved the way for malicious actors to exploit vulnerabilities, especially through the increased use of remote work tools like RDP (Remote Desktop Protocol).
Organizations must proactively address the evolving data security challenges to safeguard their sensitive information and mitigate potential financial and reputational damages in this dynamic landscape.
The convergence of public cloud services and remote work necessitates a comprehensive and adaptable approach to protect against cyber threats. We’ll discuss the major cloud security concerns and ways to overcome them.
Related: 5 Benefits of Custom Data Management Solutions for Your Business
The use of personal devices for work purposes
Using personal devices in the workplace poses a security risk. While using one device for personal and professional needs is convenient, we must remember the potential for data breaches.
To protect your business, be proactive and vigilant. Implement a strong BYOD policy to maintain a balance between convenience and security.
BYOD policies have their pros and cons. They offer convenience but also bring security concerns. Using personal devices for work can increase productivity and cut costs. However, it can also lead to data breaches and unauthorized access.
Unsanctioned devices are vulnerable to lurking threats. You must understand the risks and implement effective BYOD policies to protect your enterprise.
Phishing schemes
Phishing is a fraudulent activity that gathers sensitive information through deceptive emails and websites. Attackers pretend to be someone or something trustworthy to trick people into giving them access to private information, which they can then use for theft or fraud. Train employees on security awareness for best results.
Security of home Wi-Fi
There is often more focus on securing the laptops used in the workforce. At the same time, the safety of home router software is frequently overlooked. Routers that need to be upgraded may not address their security vulnerabilities, potentially increasing the risk of data breaches over an extended period.
It has been observed that many individuals need a firewall to ensure the security of their home network. Regular updates to the router software are necessary to address the issue. Additionally, certain routers offer various encryption capabilities that may be enabled.
A security gateway is recommended for professionals who handle sensitive data.
Passwords
Although cyber security software has been implemented, employees’ use of easily guessable passwords still poses a risk due to human error. Hackers use different ways to gain access to passwords.
Additionally, individuals may develop code to systematically try different combinations to crack a password. Over time, the bot may gain the ability to access users’ accounts.
Implementing a password policy is considered the most effective approach. Passphrases are advisable to enhance security and prohibit using personal data and repeated passwords for login purposes.
Sharing files without encryption
Your employees regularly handle sensitive information such as client’s personal details and financial data. Encrypting information during transition is as important as encrypting it while stored on the network.
When sensitive data is captured by third parties, it can lead to various negative outcomes, such as identity fraud, theft, and malicious attacks.
To effectively overcome cloud security risks, you should hire a team of qualified IT specialists with hands-on experience in cloud computing. How to find them? You can think of the in-house vs. outsourcing software development opportunity and find all the answers to your questions.
Related: Software Testing Consulting Benefits for Healthcare Business
The Hidden Security Risks of Cloud Computing You Need to Know
If you’re moving data to the cloud, it’s important to know about the security risks that come with it. To protect your business, here are the top ten risks associated with cloud computing that you need to watch out for.
One of the top security risks in cloud computing is poor access management. Hackers are increasingly targeting this area as having access to information is crucial. To prevent this, two effective measures are using multi-factor authentication and implementing a separate layout for access management on the service side.
Data loss is a serious threat that is difficult to predict and deal with. It can happen due to loss of access, deletion, or modification of data. To avoid this issue, consider implementing backups and geodiversity as preventive measures.
Insecure API is another widespread cloud threat. To prevent problems with API, performing penetration testing, providing general software security audits, applying SSL encryption and using multi-factor authentication are all recommended practices.
A data breach is a security incident where individuals without authorization obtain and retrieve information, which can lead to the leaking of data.
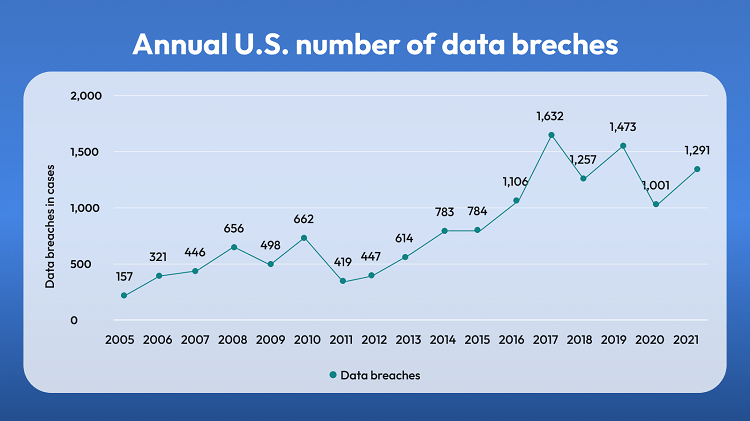
The annual number of US data breaches by years
Cloud misconfiguration occurs when a company’s cloud system is improperly configured, leaving it susceptible to security breaches.
A denial-of-service attack (DoS) is designed to block users from accessing a system or disrupting their work processes.
Malware infections. Enterprises are at risk of cyber threats when they transfer private data to the internet-connected cloud environment. To protect against malware, it is recommended to keep computers and software updated, restrict file-sharing, and use antivirus software.
Summing Up
Cloud security is quite an essential thing to think about. However, it would be best if you were technically experienced in solving all the issues connected to cloud security. You can apply to a skilled software development company to facilitate your job.
The specialists will answer all the tech questions that disturb you and assist in taking robust security measures for your business data.
Author’s bio:
Yuliya Melnik is a technical writer at Cleveroad. It is a web and MOBILE APP DEVELOPMENT COMPANY in Ukraine. She is passionate about innovative technologies that improve the world and loves creating content that evokes vivid emotions.